On December 2, ICS-CERT pushed an update to a vulnerability advisory for Emerson ROC RTUs. The original advisory was published on September 26, 2013.
Most ICS-CERT advisory updates include incremental information, such as the vendor identified more vulnerable versions, or the vendor released a patch. When you open up the Emerson ROC vulnerability update that is the impression you get:
So, when you read this, you believe that Emerson has released a patch and that the patch has been validated by the researchers who disclosed the vulnerabilities. Seems simple enough.
But keep reading and you see that the little update wasn’t so little:
Capture replay is a HUGE deal. Essentially this means that a lack of authentication for communications allows an attacker to send the vulnerable RTU whatever commands he had previously recorded.
But it’s okay, because it has been patched right? I mean “Update A part 1 of 3” says in direct terms:
Emerson Process Management has produced a patch that mitigates these vulnerabilities.
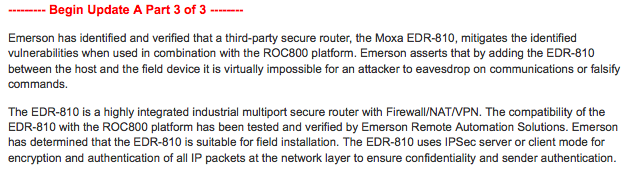
Well, keep plowing into the depths of the document, because you may never guess what’s coming next:
That’s right: There is no patch! This could be interpreted to mean that there is no patch. You need may actually need to install another device on your network to mitigate the issue.
My conclusion: Many vulnerability communications are not serving the needs and interests of firms that are actually operating critical infrastructure.
Critical Intelligence conducts its own analysis of every ICS vulnerability it comes across to make sure the utilities, water facilities, and refineries operating industrial systems:
- Don’t miss publicly disclosed vulnerabilities
- Don’t get lost in the details
- Accurately understand the possible impacts to the processes they run
If you are really trying to protect critical infrastructure, then you’ve got to communicate clearly. To get that type of communication, subscribe to the Core ICS Intelligence Service.
UPDATE Dec. 18, 2014: ICS-CERT now confirms that the Emerson patch did not address the capture-replay attack.